A Printer’s Guide to Digital Print Embellishment
Professional printing used to be all about putting simple text on paper, but that’s changed. Now, it’s all about br…
Why Do Print Assessments for Managed Print Programs?
Any managed print provider worth their salt will want to do an initial print assessment before they propose any cha…
Meet the Marco Technology Assessment
Yes. We know — most “technology assessments” are very different. Ours isn’t just a simple scan, where we spit out a…
Business Collaboration Technologies Worth Implementing
Over the past four years, we've fundamentally shifted what it means to be a workplace, and for many of us, our comm…
How Managed Print Helps With Regulation and Standards Compliance
To put it bluntly, regulatory agencies are no longer playing around. Failure to comply can result in increasingly h…
Why Your Business Needs Microsoft Intune
Regardless of whether you’ve fully returned to in-person work or you’ve embraced a hybrid model — or what your mobi…
What Is Happening to Microsoft Teams?
On April 1, 2024, Microsoft announced that moving forward, commercial Microsoft 365 and Office 365 suites won’t inc…
Cloud vs. On-Premises Communications [Infographic]
Even though there are a wealth of blogs online titled, “The best communication solution for businesses,” there’s re…
Choosing Your Next Business Phone System
A potential customer finds your business online, checks out your website, and thinks you might be able to help them…






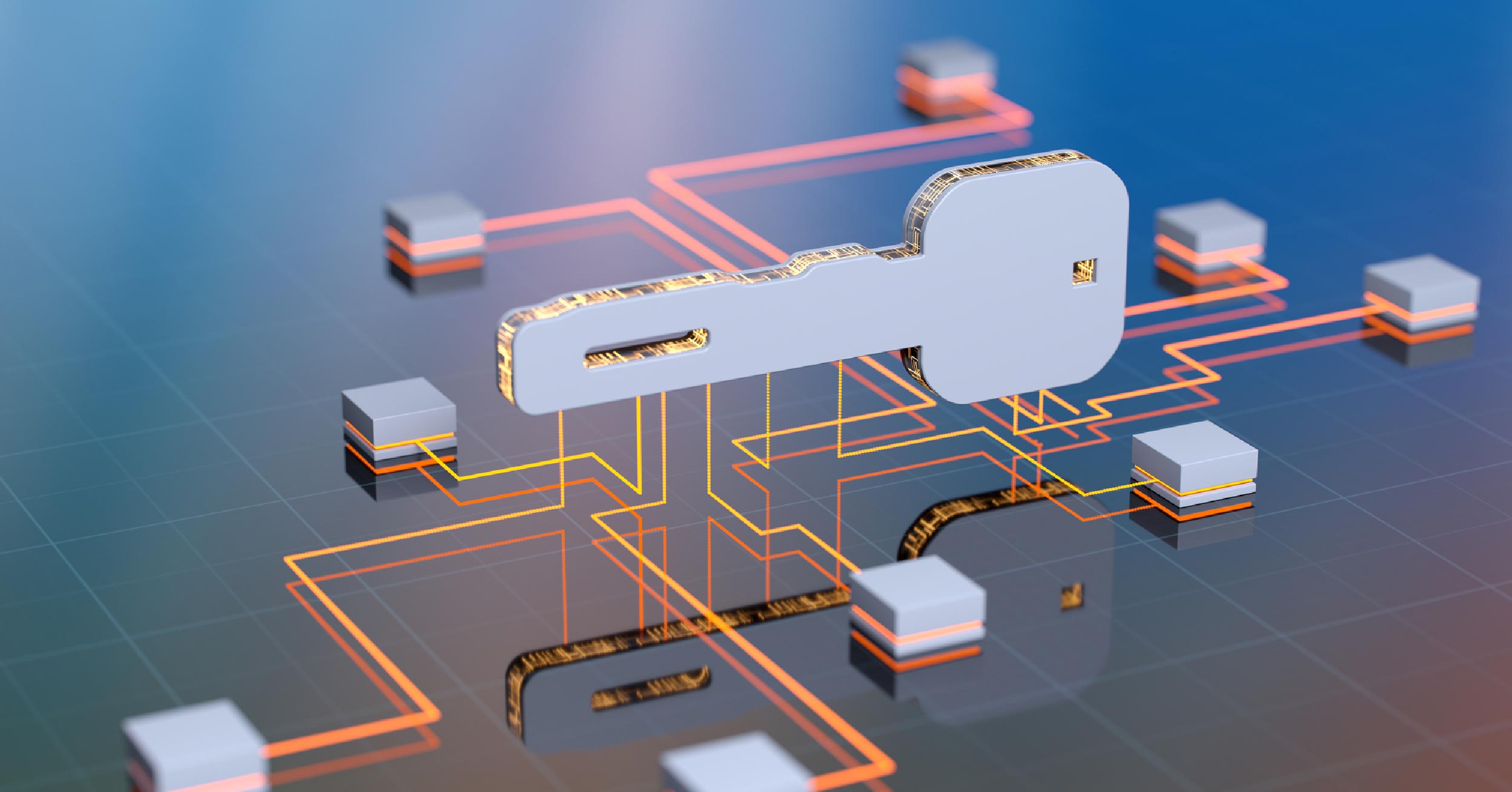

![Cloud vs. On-Premises Communications [Infographic]](https://www.marconet.com/hubfs/UCaaS-infographic.jpg)
